Awareness Training
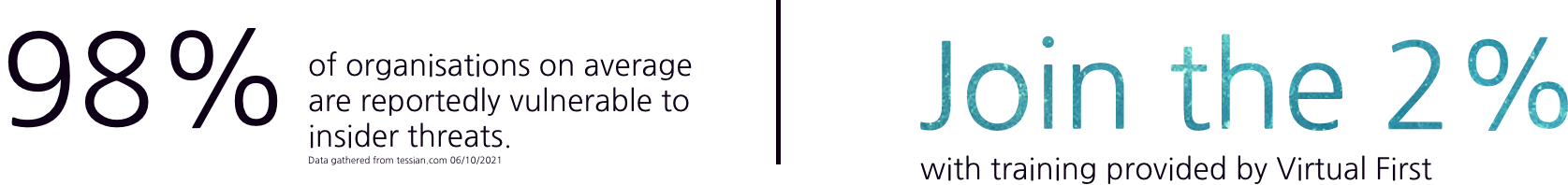
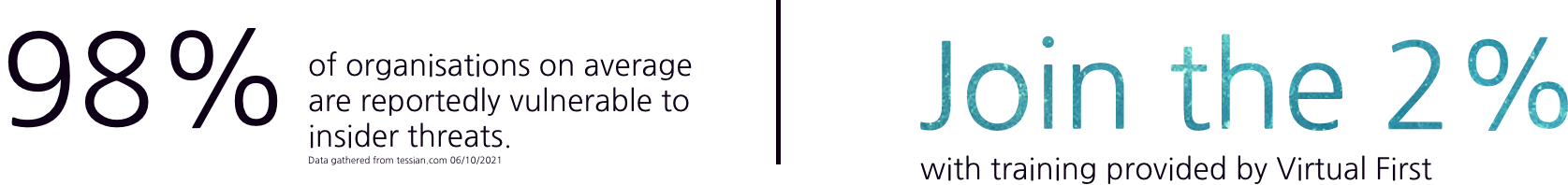
Cyber attacks do not only come externally, they can come internally too and it is for this reason why your staff need to recognise suspicious activity and mitigate it before any threats pose a real risk to your network.
Adopt engaging bite-sized courses to help educate your team using an effortless learning framework. Reinforce educational material and track your teams’ development.
Gain access to a broad range of courses to ensure you cover the awareness training you need. Enable your staff to recognise incoming threats and respond appropriately to eliminate the risk.
Infrastructure Penetration Testing
Audit your IT infrastructure’s integrity utilising rigorous testing of your network’s security. This assessment will conduct simulated cyber attacks that will push to breach your security protection.
The testing would be a controlled form of hacking that will determine and identify any vulnerabilities to your cyber security. The simulation would adopt advanced techniques and tools to impersonate a realistic attack on your IT infrastructure.
After the assessment has been conducted, you will be provided with a thorough report that highlights your cyber security’s current state, what and where the vulnerabilities are situated along with guidance on securing your business’s exposures and mitigating risk.


Vulnerability Assessment
Using manual and automated testing, the assessment will explore your IT infrastructure and discover any current exposures without exploiting them.
Cyber attackers are consistently exploring opportunities in taking advantage of vulnerabilities in corporate networks.
This assessment allows you to take a more proactive approach to safeguarding your business, identifying and mitigating any posing risks to your infrastructure.
The reporting from this assessment will enable your IT team to act rapidly to any network exposures with a remediation process to hand.


Simulated Phishing Assessment
When it comes to data breaches, the most reported cause is down to successful phishing attacks. All it takes is for one successful phishing attempt to expose your IT infrastructure which is why your staff need to be vigilant and able to remediate any phishing attempts they receive.
Although there are autonomous measures in place to help mitigate phishing like email filters, they can only prevent up-to quarter of attempts, the rest are received by your staff and it is down to them to uphold the security of your infrastructure.
The assessment trains your workforce by simulating realistic phishing attempts to conduct practical learning assessments in educating your team.
By engaging with your workforce with simulated experiences, they can quickly learn to recognise phishing attempts and understand where they themselves can pose a threat to your cyber security. You will be able to monitor their development and have visibility on your risk to phishing before training compared to after.


Cyber Essentials Plus
Qualify your business with a UK government approved certification that demonstrates your commitment to cyber security which reassures others of your operational protection.
Review your digital security against a broad range of threats and recieve an accreditation that verifies a in-depth technical assessment approval that has thoroughly tested your defence.
Educate yourself and better protect your business whilst reassuring your customers that their information is protected with advanced security measures.

